
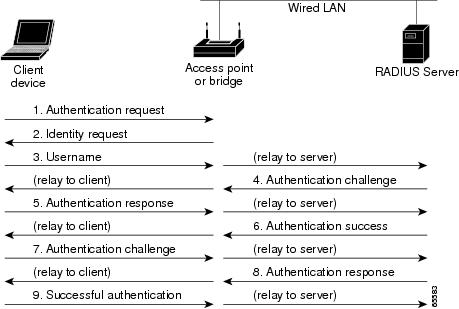
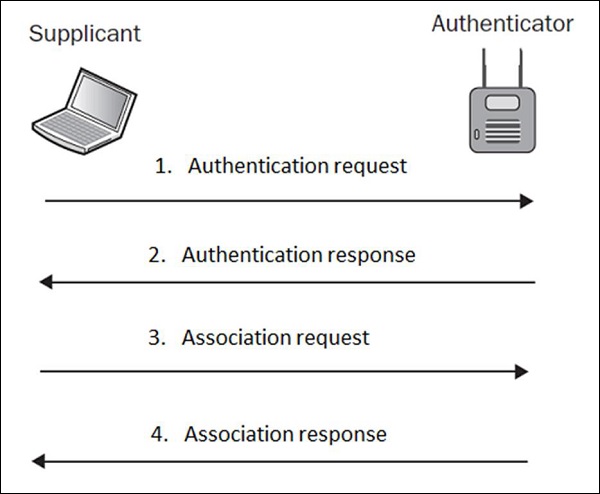
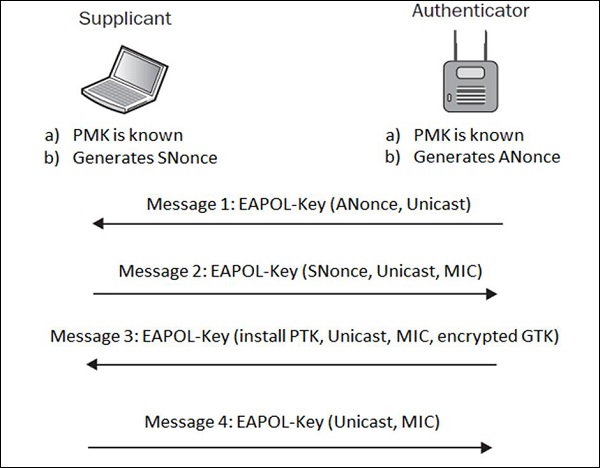
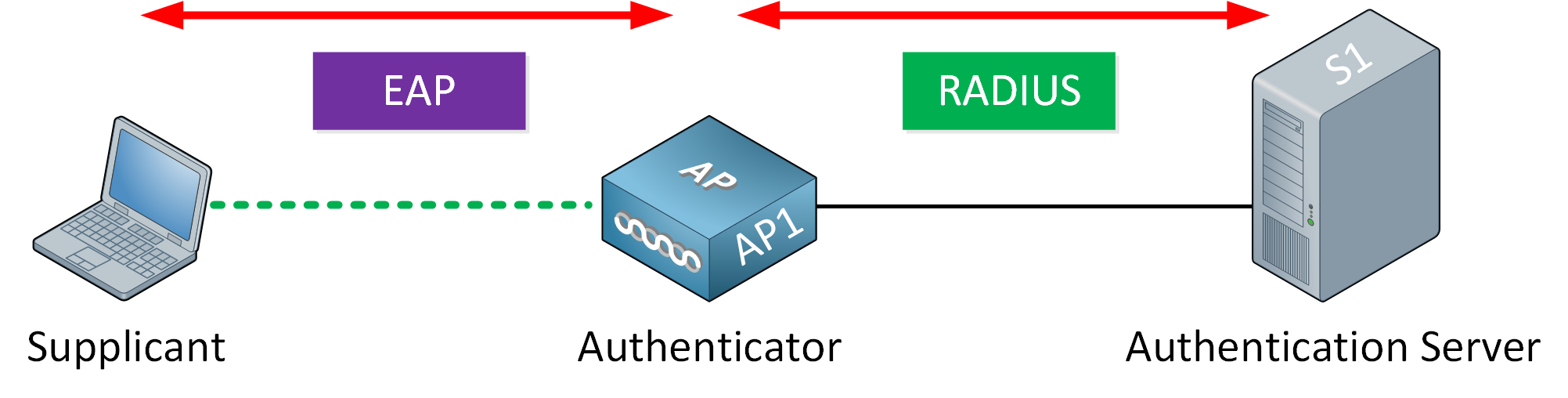
The authentication methods are encapsulated within the above messages.... | Download Scientific Diagram

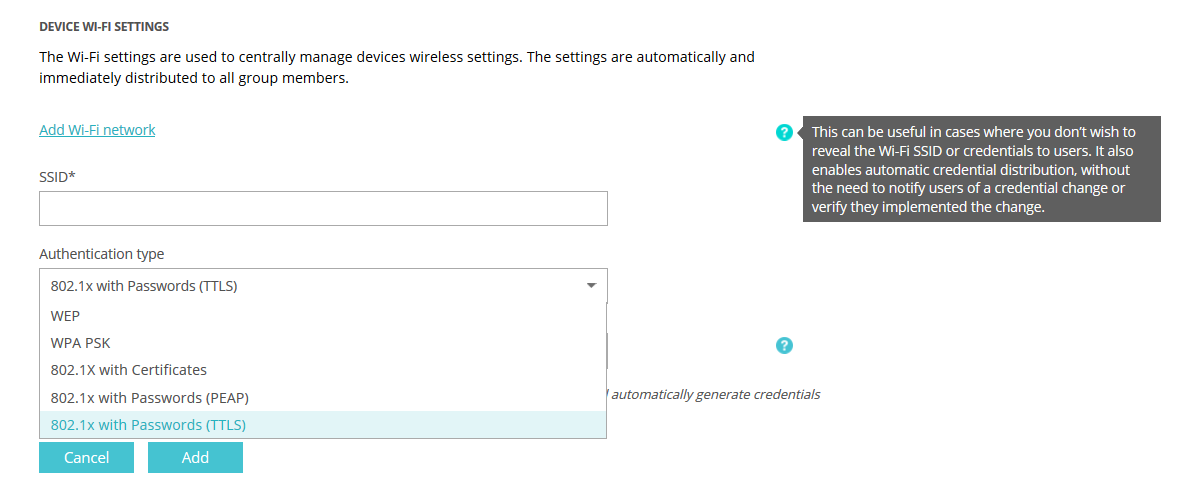
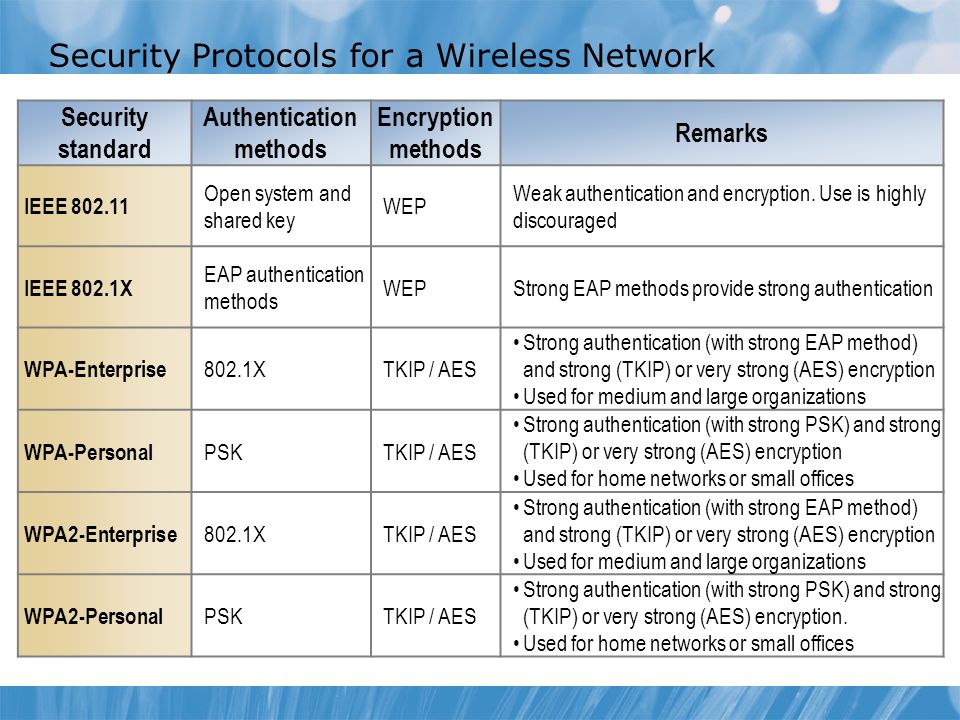
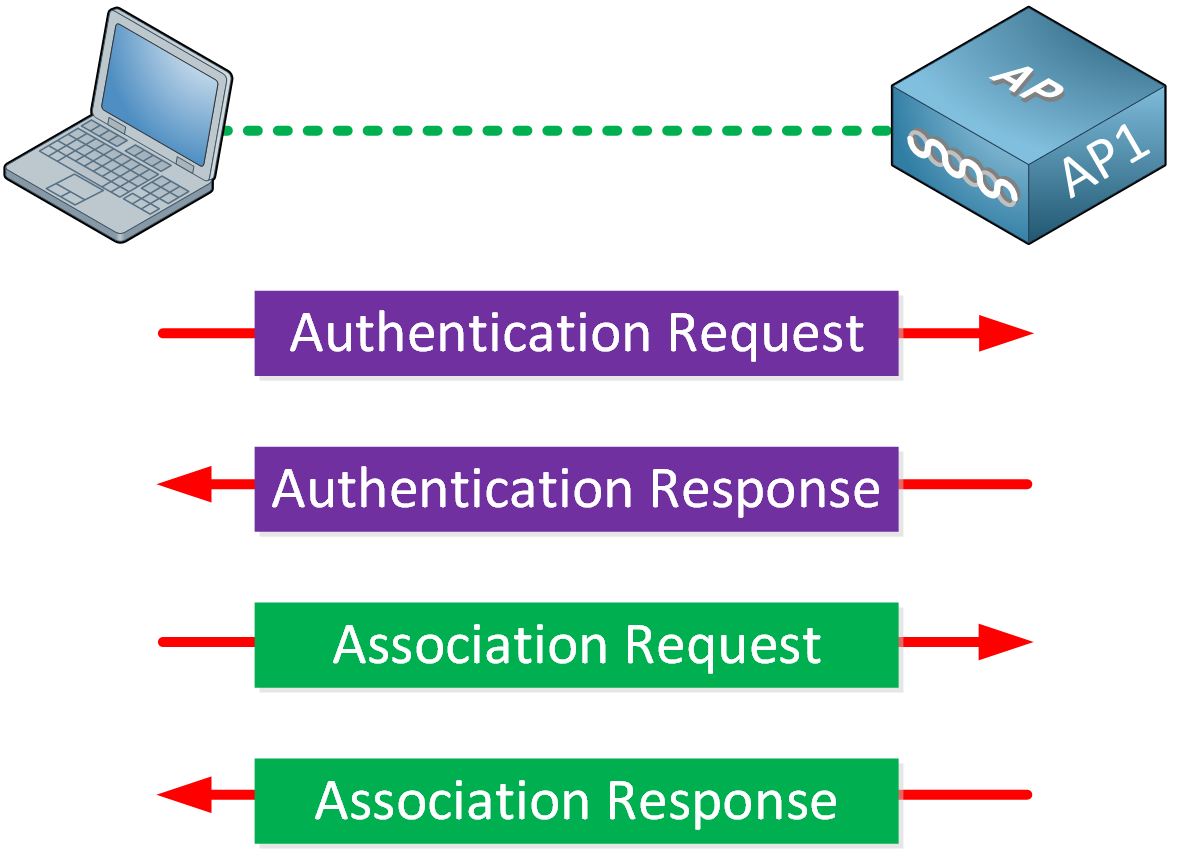
Understanding WLAN Security Policies - Wireless Access Controller (AC and Fit AP) V200R008C10 CLI-based Configuration Guide - Huawei
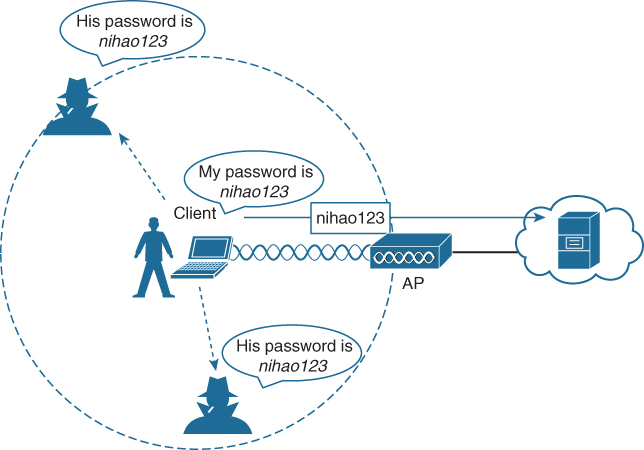
Pass-through Authenticator The authentication methods are facing to... | Download Scientific Diagram







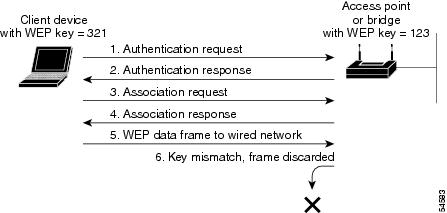
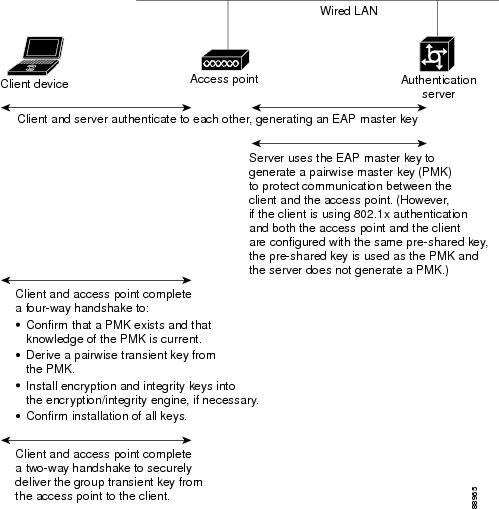
![802.11 Network Security Fundamentals [Cisco Secure Services Client] - Cisco Systems 802.11 Network Security Fundamentals [Cisco Secure Services Client] - Cisco Systems](https://www.cisco.com/en/US/i/200001-300000/270001-280000/270001-271000/270661.jpg)